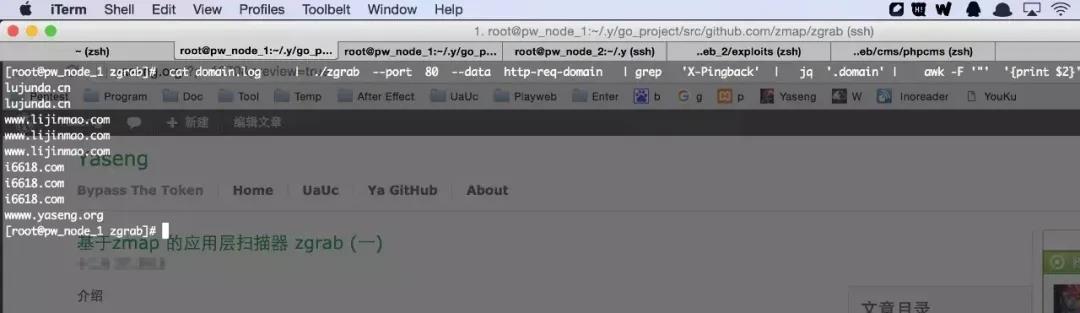
zgrab 是基于zmap无状态扫描的应用层扫描器,可以自定义数据包,以及ip,domain之间的关联。可用于快速指纹识别爆破等场景。 go环境 zgrab go get github.com/zmap/zgrab cd $GOPATH/src/github.com/zmap/zgrab go build zmap -p 443 --output-fields=* | ztee results.csv | zgrab --port 443 --tls --data=./http-req --output-file=ban 其中 http-req 为自定义的数据包。 [root@pw_node_1 zgrab]# cat http-req GET / HTTP/1.1 Host: %s 域名列表 ip,domain 的文件,例如 : [root@pw_node_1 zgrab]# cat 2.csv36.51.255.148,tinyjun.com 36.51.255.148,i6618.com 36.51.255.148,www.linwen.com 36.51.255.148,lujunda.cn 36.51.255.148,haohaomai.com 36.51.255.148,it1208.com 36.51.255.148,www.lijinmao.com 36.51.255.148,lushao.cn 36.51.255.148,i6618.com 36.51.255.148,www.it-case.com 36.51.255.148,zhihub.com 36.51.255.148,wwww.yaseng.org 默认输出为json ,可以使用jq 工具解析。 扫描 127.0.0.1,localhost 效果如图。 命令行: [root@pw_node_1 zgrab]# cat 3.csv127.0.0.1,localhost [root@pw_node_1 zgrab]# cat /tmp/3.csv | ./zgrab --port 80 --data http-req-domain | jq "."{ "data": { "write": "GET / HTTP/1.1\r\nHost: localhost\r\n\r\n", "read": "HTTP/1.1 200 OK\r\nDate: Sun, 27 Dec 2015 17:33:43 GMT\r\nServer: Apache/2.2.15 (CentOS)\r\nLast-Modified: Fri, 11 Dec 2015 14:51:21 GMT\r\nETag: \"82db1-e-526a074ea5571\"\r\nAccept-Ranges: bytes\r\nContent-Length: 14\r\nConnection: close\r\nContent-Type: text/html; charset=UTF-8\r\n\r\nhello yaseng\n" }, "timestamp": "2015-12-28T01:33:43+08:00", "domain": "localhost", "ip": "127.0.0.1"} { "sni_support": true, "ca_file_name": null, "mail_type": null, "tls_version": null, "timeout": 10, "port": 80, "success_count": 1, "failure_count": 0, "total": 1, "start_time": "2015-12-28T01:33:43+08:00", "end_time": "2015-12-28T01:33:43+08:00", "duration": 0, "senders": 1000 } [root@pw_node_1 zgrab]# curl localhosthello yaseng [root@pw_node_1 zgrab]# 可以自定义http 数据包,例如: [root@pw_node_1 zgrab]# cat http-req-domainGET /1.php HTTP/1.1 Host: %d 例如需要在一大批域名列表里面快速识别wordpress,并且输出域名。首先从header 里面找出wp 的指纹以。 [root@pw_node_1 zgrab]# curl -I yaseng.orgHTTP/1.1 200 OK Server: nginx/1.2.6 Date: Sun, 27 Dec 2015 17:59:25 GMT Content-Type: text/html; charset=UTF-8 Connection: keep-alive Expires: Thu, 19 Nov 1981 08:52:00 GMT Cache-Control: no-store, no-cache, must-revalidate, post-check=0, pre-check=0 Pragma: no-cache X-Pingback: http://yaseng.org/xmlrpc.php Via: 10.17.21.22 Set-Cookie: saeut=11111151239164757346; path=/; max-age=311040000 Set-Cookie: PHPSESSID=86483bb31b614b6f5a9513854a27e321; path=/; HttpOnly 使用 字符串 X-Pingback 来做识别指纹 识别命令为: cat domain.log | ./zgrab --port 80 --data http-req-domain | grep 'X-Pingback' | jq '.domain' | awk -F '"' '{print $2}'2
3
参数 注释 示范 port 端口 --port 80 data 发送数据包并且返回响应 --data http-req-domain 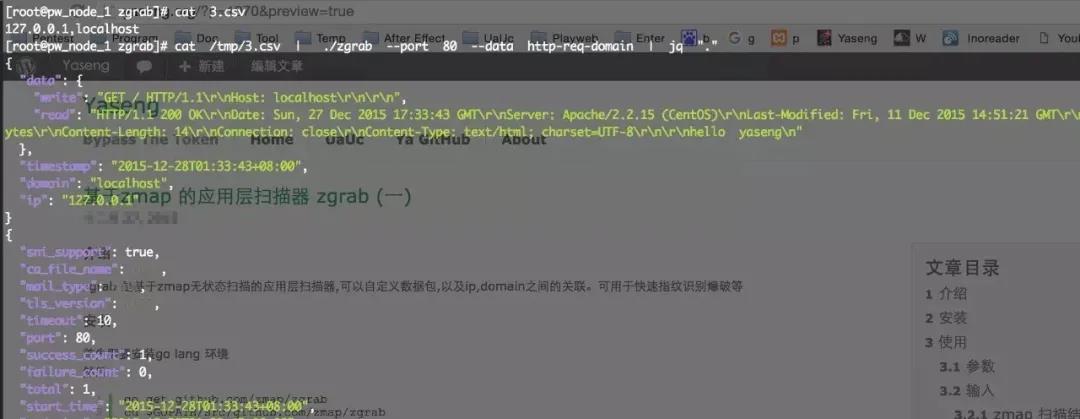
4